What is a“deepfake” cyberattack?
We already explained it as a risk of the use of AI in CEO Fraud cyberattacks. But in general, e n the Internet, it is increasingly difficult to distinguish what is real from what is not. Videos deepfake have become one of the most sophisticated techniques in the creation of fake news.
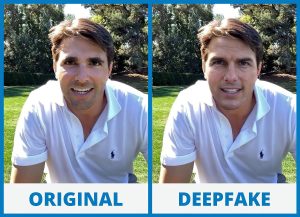
The word deepfake unites two terms: deep learning y fake. The first refers to the deep learningone of the branches of artificial intelligence. The second, already known to all, means “false” and refers to the creation of fake news. In short, they are manipulated videos that make users believe that a person is carrying out an action that has never taken place.
One of the main problems of deepfakes deepfakes is the use made of them to manipulate information. If a fake news story is dangerous, a video is even more so; it is given more credibility and goes viral faster.
It is easy to create this type of content because there are applications, with artificial intelligence technology, that make it possible to make changes in people’s faces and voices.
In this sense, we can talk about two types of deepfakes:
- Deepface: Superimposing one person’s face on another person’s face and falsifying gestures.
- Deepvoice: single sentences of a person are joined together to create a false speech.
Like the fake news to use, these videos generate disinformation. But they can also be dangerous for your cybersecurity (cybercriminals could steal your credentials or infect your devices).
How can we detect it? Pay attention and don’t fall into their traps!
- Applying common sense. Depending on the live conversation or the video we are watching, it is possible that the message may give us to understand that it is a fraud.
- When in doubt, be wary of everything. It is preferable not to give credibility to all the videos we see on the Internet and to contrast the information by other means.
- Be alert to image and voice distortions. These impersonations are not yet perfect. So if we see a video impersonating the image and voice of a public person or we receive a video call supposedly from an acquaintance (boss, friend, family member) at the minimum that we see any problem in the image or voice, we should be suspicious and cut that communication.
- Double checking never fails. In the latter case, when the cyberattack is used with a close person, it is preferable to contact that person by a different means to confirm that the video call or video is real and reliable.
IMPORTANT NOTE: If, even while complying with all these measures, you encounter situations that do not conform to the level of security required or established in internal policies, do not hesitate to report it to your line manager, the Security Manager, security personnel and/or the IT department, depending on the type of suspicion. If it happens to you on a personal level, report it directly to law enforcement authorities, so that they can advise you appropriately and conduct an investigation.
*Shipment date: June 30, 2025